Azure Infrastructure
This page provides an overview of the cloud infrastructure for wastelog-vnet, deployed in the Switzerland North Azure region. The setup includes a public entry point, and fully isolated, private environments for both Development and Production.
Architecture Overview
The network is separated into public and private subnets to logically divide roles, networking, and security.
- Region: Switzerland North
- VNet Name:
wastelog-vnet - Address Space: 10.0.0.0/16 (spread across subnets)
Diagram
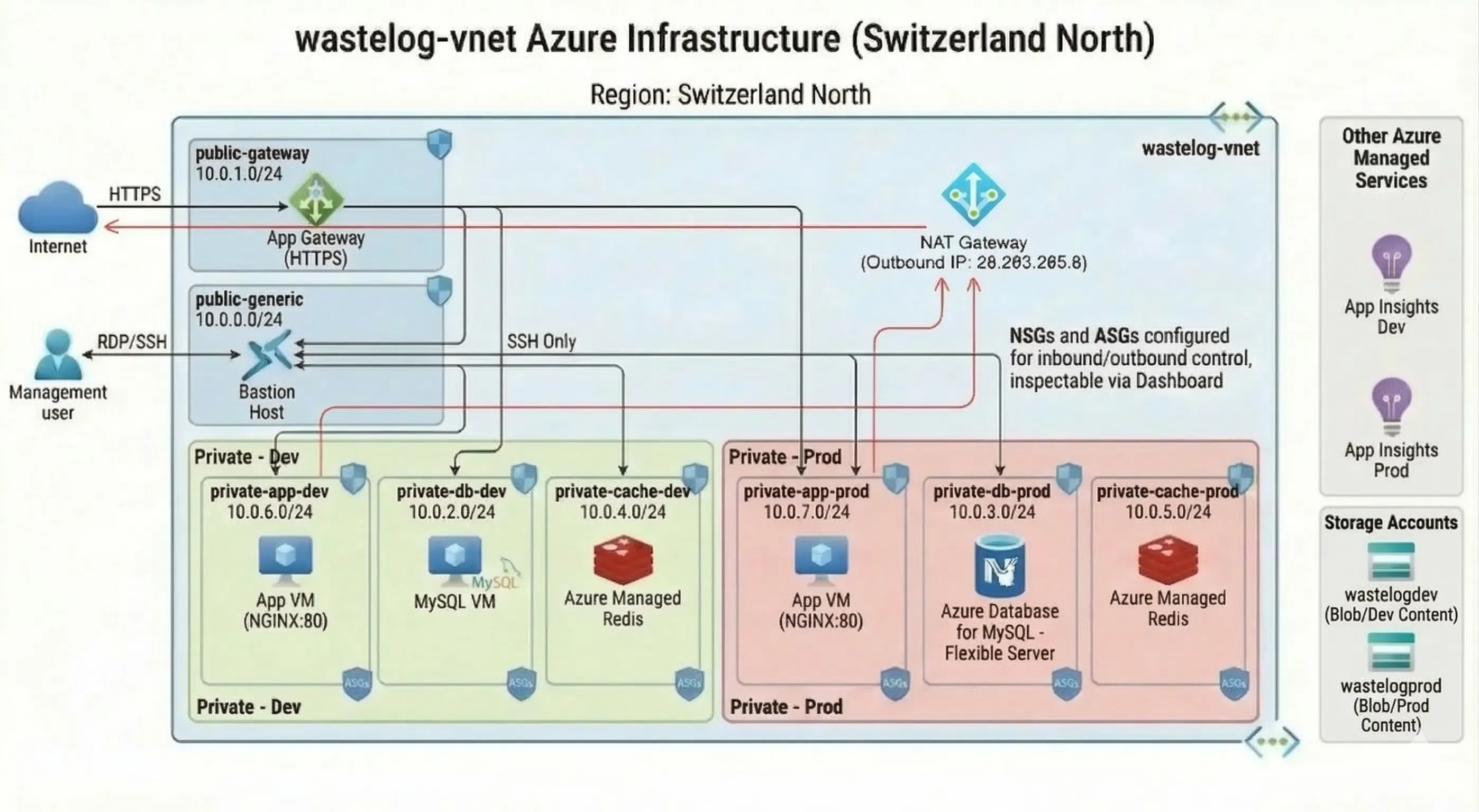
Network Topology
The Virtual Network is divided into multiple subnets, each serving different roles:
| Environment | Subnet Name | CIDR | Resource Type | Notes |
|---|---|---|---|---|
| General | public-gateway | 10.0.1.0/24 | App Gateway | Entry point (HTTPS) |
| General | public-generic | 10.0.0.0/24 | Bastion Host | Management access |
| Dev | private-app-dev | 10.0.6.0/24 | Virtual Machine | NGINX Web Server (1 node) |
| Dev | private-db-dev | 10.0.2.0/24 | Virtual Machine | MySQL Server |
| Dev | private-cache-dev | 10.0.4.0/24 | Managed Redis | Caching layer |
| Prod | private-app-prod | 10.0.7.0/24 | Virtual Machine | NGINX Web Server (1 node) |
| Prod | private-db-prod | 10.0.3.0/24 | Azure Managed MySQL Flexible Server | MySQL Flexible Server |
| Prod | private-cache-prod | 10.0.5.0/24 | Managed Redis | Caching layer |
Component Details
1. Entry & Connectivity
- App Gateway: Receives all inbound HTTPS traffic from the internet and distributes requests to the corresponding backend pool (Dev or Prod).
- Bastion Host: A dedicated virtual machine in the public subnet, used for secure SSH/RDP access to the private VMs. Direct internet access to private VMs is not allowed.
2. Compute (Application Layer)
Both Dev and Prod environments utilize NGINX running on Virtual Machines, serving HTTP on port 80.
- Scaling: Each environment currently uses a single VM node.
3. Data Persistence
- Database:
- Development: MySQL is hosted on a Virtual Machine.
- Production: Azure Managed MySQL Flexible Server is used.
- Note: Due to capacity limits in Switzerland North, only the Dev environment runs MySQL on a VM, while Prod uses the managed database.
- Cache: Azure Managed Redis provides high-performance caching.
- Storage: Azure Blob Storage is used for object storage (e.g., admob data).
4. Observability
- Application Insights: Integrated in both environments for performance monitoring and error analysis.
5. Security
- NSGs (Network Security Groups): Attached to subnets to filter network traffic (allow/deny).
- ASGs (Application Security Groups): Used to group VMs and manage security at a granular level.
Deploying a Temporary Bot VM or Similar General VM
If you need to deploy a temporary bot VM or similar server with general access, you can use the public-generic subnet. Make sure to update the Network Security Group (NSG) assigned to the subnet to follow the latest security rules. The relevant NSG for this case is vm-app-dev-nsg. Below is a visual sample of the NSG rules:
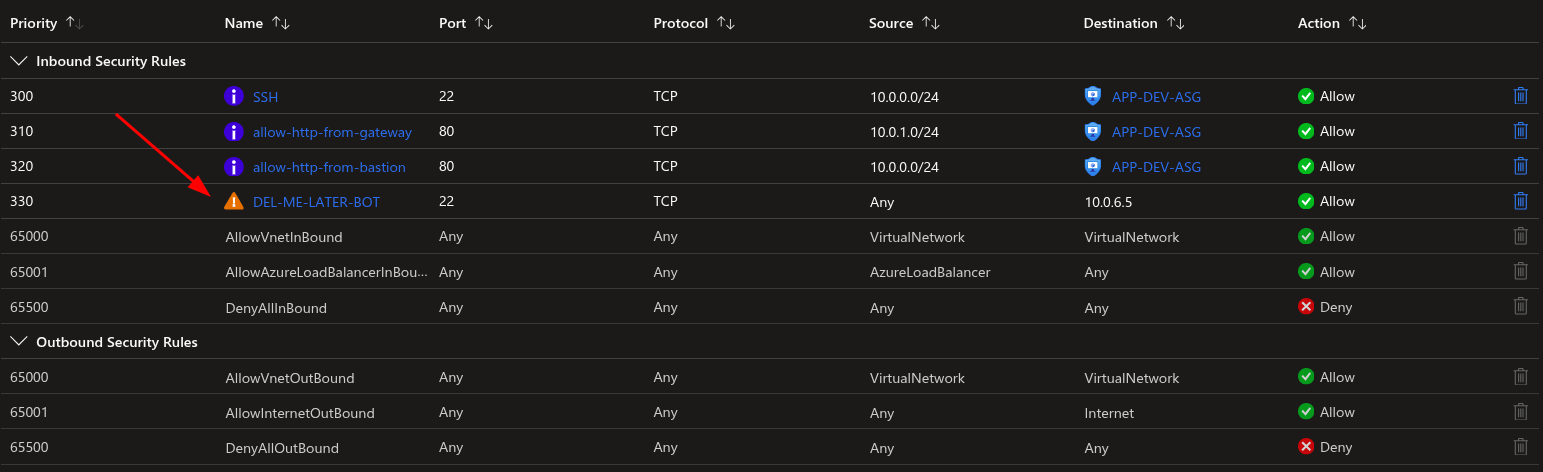
Note: Only open necessary ports/services. Avoid permitting unnecessary traffic for security reasons.